Discover Your Favorite Baseball Memories
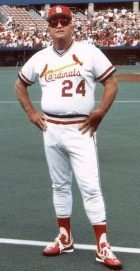
Bob Gibson fans the Reds’ Cesar Geronimo to become the second hurler after Walter Johnson to strike out 3,000 batters
Eddie Plank of the Federal League’s St. Louis Terriers records his300th victory when he defeats the Newark Peppers 12-5. The future Hall of Famer (1946) is the ninth player and first southpaw to reach this milestone.
Recommended
Trending News
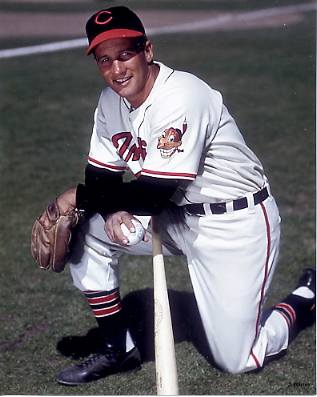
Al Rosen is named as a unanimous AL MVP
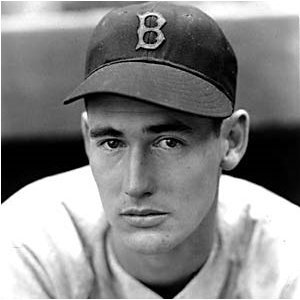
Ted Williams, who lost the Triple Crown when his batting average was .0002 below that of George Kell, wins the American League MVP Award vote in a landslide
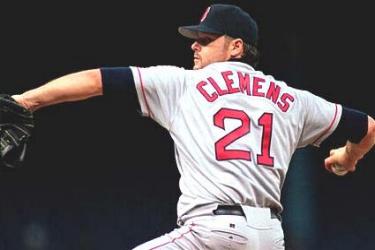
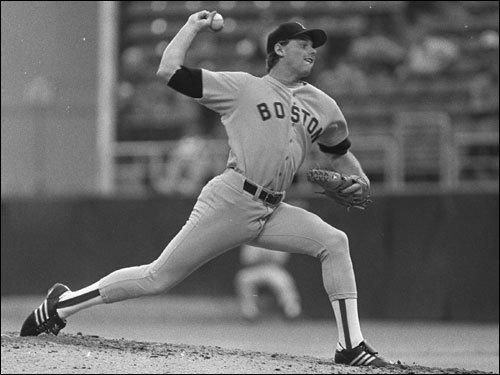
The Tigers’ Justin Verlander wins the American League Most Valuable Player Award the first starter since Roger Clemens in 1986
Alex Rodriguez wins the American League MVP Award for the second time in three seasons
Yankee catcher Thurman Munson wins 1976 AL Most Valuable Player
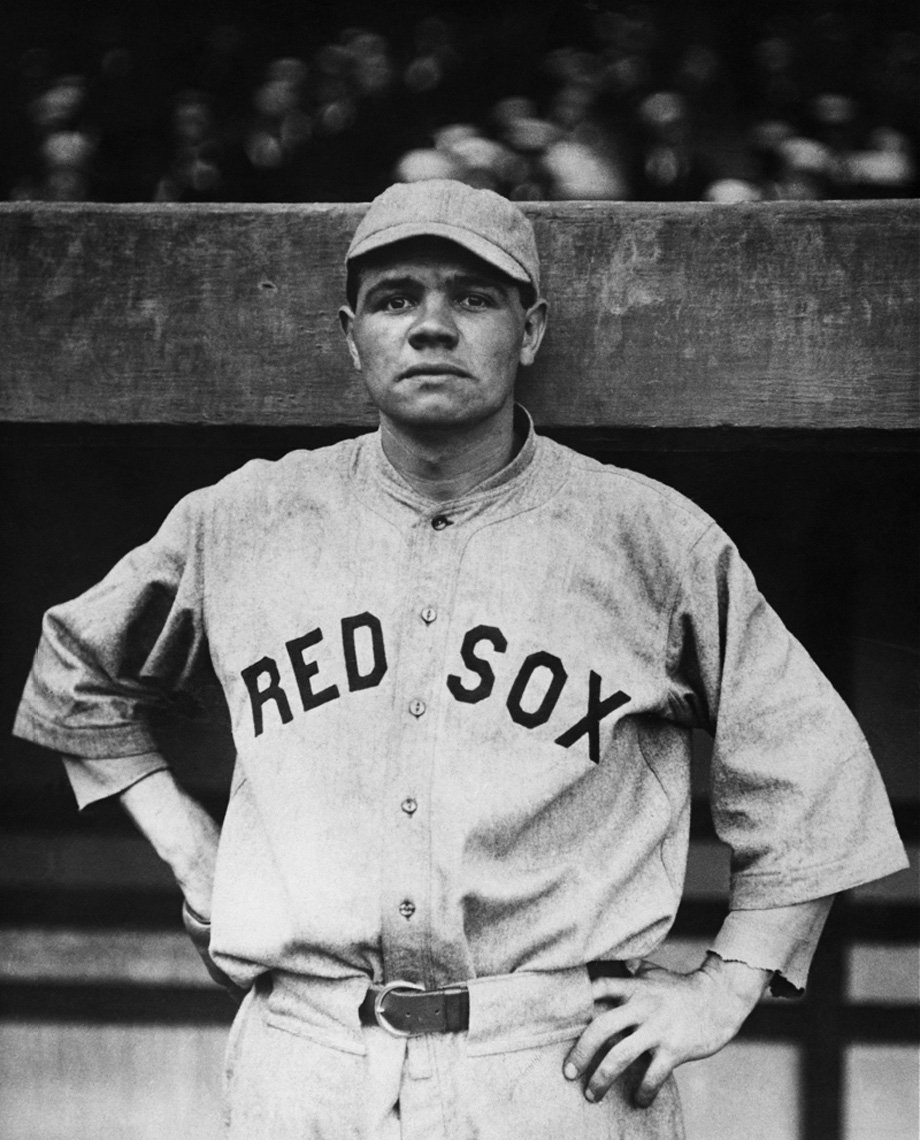
Ted Williams of the Boston Red Sox wins his first Most Valuable Player Award
-
College Baseball Teams: A Complete List of Schools for Future Students
Navigating the vast landscape of college baseball can be as challenging as hitting a curveball. With hundreds of institutions offering baseball programs across various divisions, future students with dreams of diamond glory need a comprehensive guide to make their college selection process as smooth as a well-oiled glove. This article outlines the tiers of college…
-
6 Budgeting Strategies You Should Master Before Wagering On The MLB
Betting on Major League Baseball (MLB) can be an exhilarating way to enhance your viewing experience, deepen your connection with the sport, and potentially earn some extra cash. However, without a solid financial strategy, the thrill of the game can quickly turn into a source of stress. Mastering a set of budgeting strategies is crucial…
-
Unique Career Opportunities in Baseball
Unique Career Opportunities in Baseball Your passion for sports needs a direction that can lead to a secure professional career. Playing baseball for fun is fine, but when you need to make it a source of income for a stable future, you have to be extra careful about your selections. Careful consideration of top careers…
-
How to Capitalize on NBA Betting Upsets
How to Capitalize on NBA Betting Upsets Imagine sitting in front of your screen, analyzing the odds for the upcoming NBA games. Among the predictions, your eyes catch a glimpse of this weeks NBA predictions and something clicks. There’s an underdog there that might just have a chance. This scenario isn’t rare in the world of sports…
-
March 14 – Spring Training Game Live Stream Pittsburgh Pirates at Baltimore Orioles
March 14 – Spring Training Game Live Stream Pittsburgh Pirates at Baltimore Orioles – 7:05pm ET
-
4 Up-and-Coming Athletes Set to Dominate This Season
As the anticipation for the upcoming season builds, the spotlight shines on a select group of athletes poised for breakthrough performances. These players, previously celebrated as top prospects, have tasted success at the Major League level through brief flashes of brilliance or sustained periods of promise. Now, standing on the precipice of greatness, they…